Protecting your meetings
Zoom offers several tools to protect your meetings, helping manage participant activity, information sharing, and more.
See why millions of people and organizations trust us with their communications.
Privacy and security are top of mind for us at Zoom. Find resources and learn how Zoom works to secure your data and protect your privacy.
Zoom offers several tools to protect your meetings, helping manage participant activity, information sharing, and more.
Communications are established using 256-bit TLS encryption and meeting, webinar and messaging Content can be encrypted using AES-256 encryption, and optional end-to-end encryption.
Zoom is committed to protecting your privacy. We've designed policies and controls to safeguard the collection, use, and disclosure of your information.
The following in-meeting security capabilities are available to the meeting host:
Encryption: Protecting your event content by encrypting the session’s video, audio, and screen sharing. This content is protected during transit with the Advanced Encryption Standard (AES) 256 using a one-time key for that specific session when using a Zoom client.
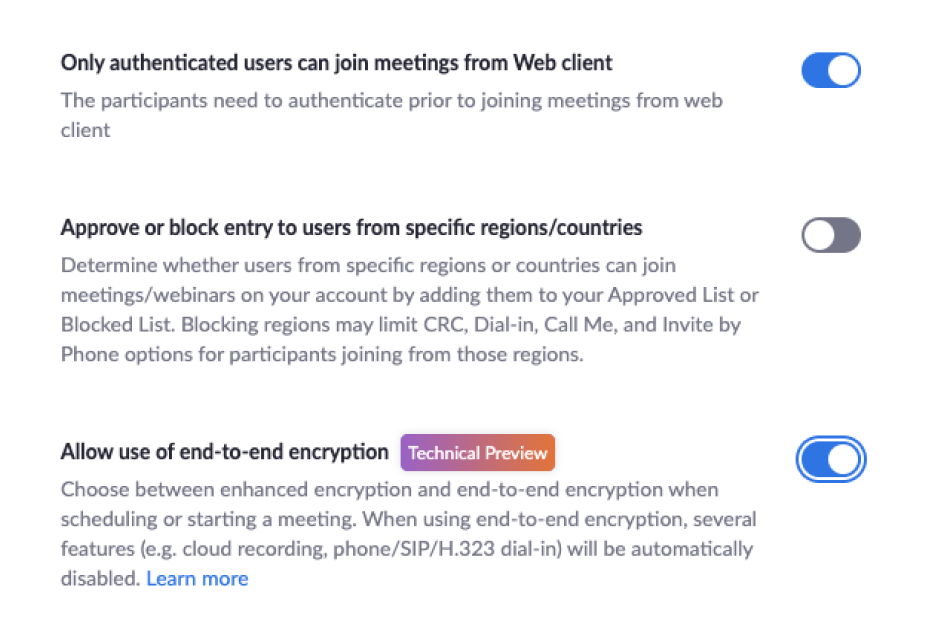
End-to-end Encryption, when enabled, ensures that communication between all meeting participants in a given meeting is encrypted using cryptographic keys known only to the devices of those participants. This ensures that no third party -- including Zoom -- has access to the meeting’s private keys.
Advanced Chat Encryption, when enabled, allows for a secured communication where only the intended recipient can read the secured message. Zoom uses both asymmetric and symmetric algorithms to encrypt the chat session. Session keys are generated with a device-unique hardware ID to avoid data being read from other devices. This ensures that the session can not be eavesdropped on or tampered with.
Zoom Phone Voicemail recordings are processed and stored in Zoom’s cloud and can be managed through the secured Zoom client.
Recordings can be stored on the host’s local device with the local recording option or on Zoom’s cloud with the Cloud Recording option (available to paying customers).
Audio Signature embeds a user's personal information into the audio as an inaudible watermark if they record during a meeting. If the audio file is shared without permission, Zoom can help identify which participant recorded the meeting.
Watermark Screenshot superimposes an image, consisting of a portion of a meeting participant’s own email address, onto the shared content they are viewing and the video of the person who is sharing their screen.
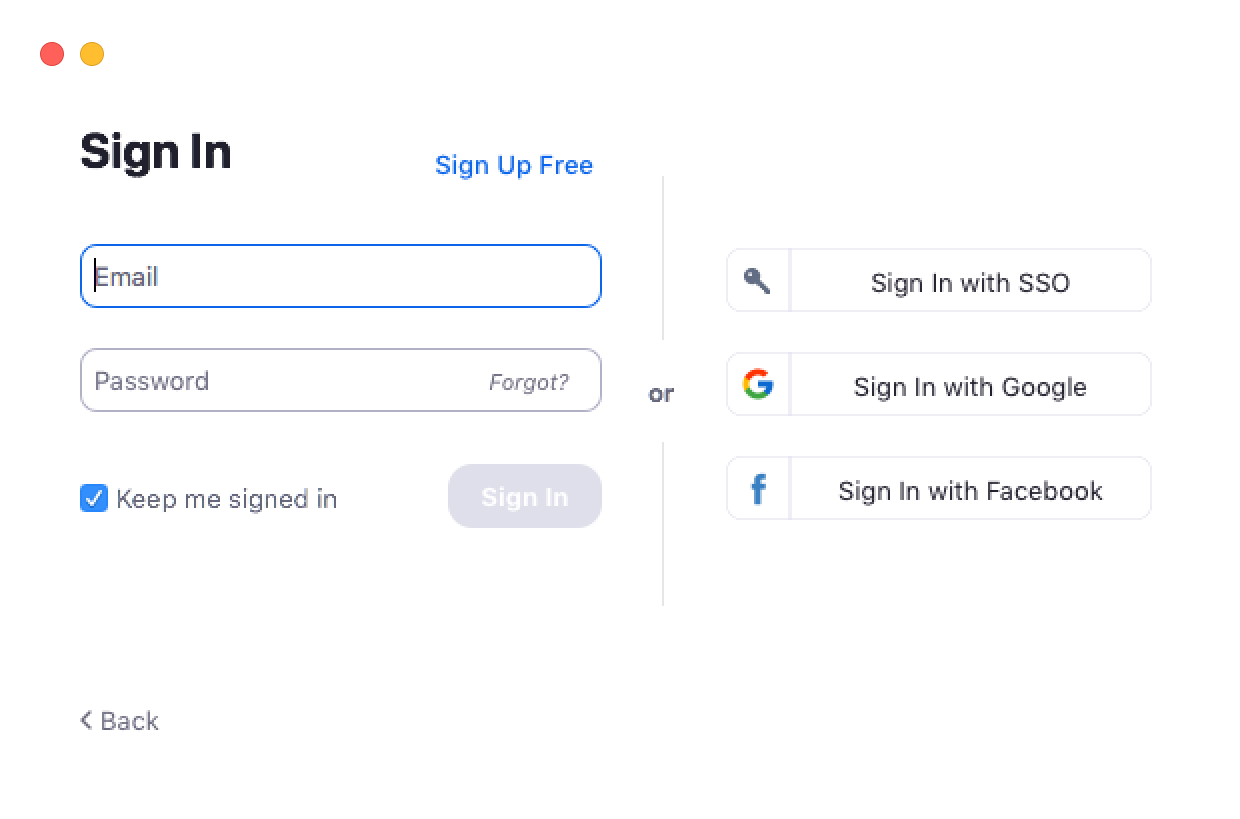
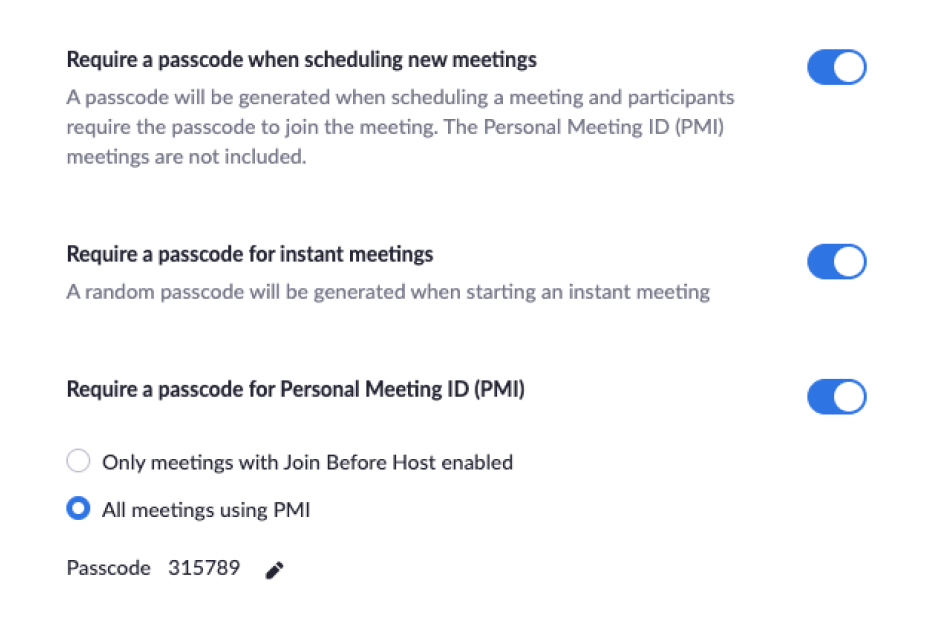
Zoom offers a range of authentication methods such as SAML, OAuth, and/or Password based which can be individually enabled/disabled for an account. Users authenticating with username and password can also enable Two-Factor Authentication (2FA) as an additional layer of security to sign in.
Zoom works with Okta as well as other enterprise identity management platforms such as Centrify, Microsoft Active Directory, Gluu, OneLogin, PingOne, Shibboleth, and many others. Zoom can map attributes to provision a user to a different group with feature controls.
OAuth-based provisioning works with Google or Facebook OAuth for instant provisioning. Zoom also offers an API call to pre-provision users from any database backend.
Additionally, your organization or university can add users to your account automatically with managed domains. Once your managed domain application is approved, all existing and new users with your email address domain will be added to your account.
Click here to learn more about Zoom’s Certifications, Standards, and Attestations.
Visit our Security Resources for more information.
If you think you have found a security vulnerability in Zoom, please visit our Vulnerability Disclosure Policy. Read more about Security Practices, Privacy Statement, Terms of Service and GDPR notice.